A structured, repeatable way to test firewall tech and prove controls work.
If you care about real security, you must test it. That is what 5.3.2 prueba de tecnologías de firewall sets out to do. In this guide, I share a clear, hands-on method to plan, run, and report a full firewall technology test. I use simple words, real examples, and hard-won lessons. You will see how to validate policy, detect threats, measure speed, and scale for cloud. By the end, you can run your own 5.3.2 prueba de tecnologías de firewall with confidence.

What is 5.3.2 prueba de tecnologías de firewall?
5.3.2 prueba de tecnologías de firewall means a formal test of firewall controls. It checks if rules, features, and logging meet your needs. It also checks if the box or service holds up under load.
This test is vendor neutral. It works for next-gen firewalls, cloud firewalls, WAF, and IPS. It works on site, in the cloud, or at the edge. It is a recipe you can reuse for each review cycle.
Think of it as a road test. You do safety checks, then drive on city roads and highways. You note speed, stops, and alerts. Then you decide if the car fits your life. The same idea drives 5.3.2 prueba de tecnologías de firewall.
Use this test to align tools to policy. Use it to compare vendors. Use it to prove due care for audits and boards.
Why this test matters now
Networks have changed fast. Apps live in clouds. Users roam. TLS hides most flows. Attackers move quick. A set-and-forget firewall is not enough.
A 5.3.2 prueba de tecnologías de firewall gives you facts. It shows what is fast, what blocks, and what fails. It turns noise into clear choices.
Key gains you can expect:
- Better policy fit because you test with your real traffic.
- Less risk because you prove block rates and see gaps.
- Lower cost because you avoid overbuying or the wrong SKU.
- Faster audits because you have repeatable results and logs.
In short, you buy and run firewalls with eyes open.
A step-by-step methodology you can trust
Here is a simple path I use in enterprise tests. It keeps teams aligned and cuts guesswork. It is the core of a solid 5.3.2 prueba de tecnologías de firewall.
- Define scope and goals. Pick apps, users, sites, and threats to test. Tie each test to a policy need.
- Set pass and fail rules. Choose KPIs like latency, block rate, and log depth. Write them down first.
- Build a clean lab. Isolate test traffic. Use time sync on all nodes. Save configs and seeds.
- Replay real traffic. Capture safe samples from your network. Scrub data. Reuse it in the lab.
- Add bad traffic. Use safe payloads to mimic malware, C2, scan, and evasion. Keep it legal and safe.
- Measure load and scale. Push line rate. Mix small and big packets. Test TLS with real ciphers.
- Inspect logs and alerts. Check time, user, app, rule hit, and action fields. Confirm you can search and export.
- Test change and drift. Update rules. Rotate certs. Fail links. Check if the firewall stays sane.
- Document results. Use a fixed template. Note gaps, fixes, and next steps.
Make each step repeatable. Version your test plan. Tag results to dates and device builds.
Lab design and tools that work
You do not need a huge lab. You need a clean one. Keep paths short. Keep clocks in sync. Use simple topologies first. Then add more links.
Useful patterns:
- Inline test with client, firewall, and server. Good for quick checks.
- Tap or span test for deep log checks.
- Hub and spoke for SD‑WAN or SASE flows.
- VPC or VNet pairs for cloud test paths.
Handy tools I use often:
- Traffic gen. iperf3 for throughput, wrk or k6 for HTTP, tcpreplay for pcap.
- Attack sim. hping3, Nmap, safely built replay pcaps, and benign payloads.
- TLS test. testssl.sh, OpenSSL s_client, and browser stacks.
- Observe. tcpdump, tshark, Zeek, and vendor logs.
- Time. NTP everywhere. A single time source saves hours.
Keep test data safe. Scrub any real user data. Rotate any keys you use.
Metrics, KPIs, and pass–fail criteria
Good tests need clear numbers. Set them before you start. Tie each number to a user or business need. That is the heart of 5.3.2 prueba de tecnologías de firewall.
Core KPIs to track:
- Throughput. How fast with features on. Measure with and without TLS inspect.
- Latency. Median and p95. Watch small packet delay.
- Connection rate. New sessions per second during spikes.
- Block rate. Percent of known bad stopped. Include evasions.
- False positives. Good traffic blocked by mistake.
- Resilience. Fail open or closed as you choose. Time to recover.
- Log quality. Fields you need are present and correct.
Set pass lines like:
- Less than 2 ms added latency for key apps.
- At least 98% block rate on test threats.
- Less than 0.5% false positives on baseline flows.
- Full logs with user, app, rule, and action in near real time.
Adjust lines for your risk and size. Record why you chose them.
Real-world test cases and lessons learned
I have run many 5.3.2 prueba de tecnologías de firewall projects. A few stories may help.
A bank had VOIP drops after a new NGFW. The box was fast on paper. In the lab we saw small packet pain when TLS inspect was on. We tuned bypass for voice subnets. Drop rate went to zero. The lesson is simple. Test with your packet mix, not vendor defaults.
A SaaS team hit high TLS handshake time. We found a weak random source in a VM host. It slowed key work. After we fixed entropy, handshake time fell by half. The lesson is to test the stack, not just the firewall.
An OT site saw false blocks on Modbus. We used clean pcaps from the plant. We wrote a custom app ID. Blocks stopped. The lesson is to bring real traffic to the lab.
Keep notes on each fix. Share with ops. Fold it back into your 5.3.2 prueba de tecnologías de firewall template.
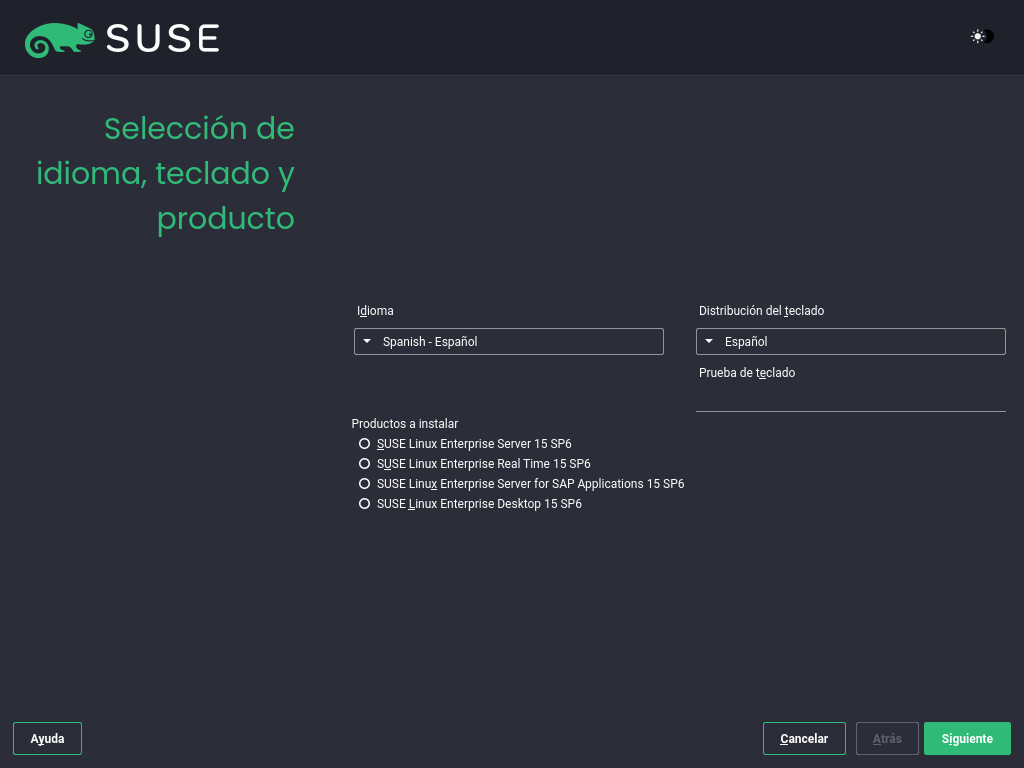
Cloud, Zero Trust, and edge cases
Cloud adds new paths. Policy sits close to apps. Identities drive rules. Edge links change shape under SD‑WAN. Your 5.3.2 prueba de tecnologías de firewall must adapt.
Tips that help:
- Test identity rules. Use groups, device posture, and MFA in flows.
- Validate east–west rules in VPCs. Use low blast radius tests.
- Check autoscale. Spin nodes up and down under load.
- Probe TLS decrypt in cloud. Mind keys, KMS roles, and lawful use.
- For SASE, test from many geos. Measure first packet time and DNS.
Do small, safe tests that mirror real user paths. Use IaC to spin labs fast. Save states so you can repeat runs.
Reporting, governance, and audit trace
A strong report builds trust. It closes the loop between tech teams and leaders. It also helps with audits and renewals.
What to include:
- Scope and goals tied to policy.
- Test setup with dates, builds, and configs.
- KPIs, charts, and raw logs.
- Gaps found and risk heat.
- Fix plan, owners, and due dates.
- A summary one page for execs.
Store the report where risk and audit can find it. Version it. Link it to change tickets. This makes your 5.3.2 prueba de tecnologías de firewall part of your normal run book.
Common mistakes and how to avoid them
I still see the same traps. Here is how to dodge them.
- Testing only at idle. Always mix real load with tests.
- Skipping TLS inspect tests. It changes all the numbers.
- Using vendor demo traffic. Use your traffic instead.
- Ignoring logs. If you cannot search it, you cannot prove it.
- No pass lines. If you do not set lines, all results blur.
Write these into your 5.3.2 prueba de tecnologías de firewall plan. Review them at each run.
Actionable checklist for your next run
Use this short list to kick off fast.
- Name owners for plan, build, run, and report.
- Freeze scope, KPIs, and pass lines.
- Build a clean, time-synced lab.
- Load real traffic pcaps and safe attack sets.
- Run baseline, feature-on, and failover rounds.
- Capture logs and packet traces.
- Score each KPI and note gaps.
- Share fixes and next steps with dates.
- Archive results for audits.
Make this your standard 5.3.2 prueba de tecnologías de firewall pack.
Frequently Asked Questions of 5.3.2 prueba de tecnologías de firewall
What does 5.3.2 prueba de tecnologías de firewall cover?
It covers policy checks, threat block, performance, and logging. It also covers change, failover, and scale.
How often should I run the test?
Run it at each major change or quarterly for high risk sites. Run a light version after every rule set change.
Do I need pricey gear to test?
No. Start with open tools and a clean lab. Add pro gear later if you need more speed or precision.
What traffic should I use?
Use real, scrubbed samples from your network. Add safe bad traffic to test block and alert.
How do I compare vendors fairly?
Use the same plan, pcaps, and KPIs for each box. Lock features to equal sets before you run.
Can I test cloud firewalls the same way?
Yes, but mind identity and autoscale. Use IaC to build and tear down cloud labs fast.
How do I handle TLS decryption in tests?
Get legal and privacy checks first. Use test certs and sample data. Record the impact on speed and latency.
Conclusion
A firewall is only as good as the proof behind it. A clear, repeatable 5.3.2 prueba de tecnologías de firewall turns claims into facts. It shows you what to buy, what to tune, and what to watch. It also builds trust with teams, leaders, and auditors.
Pick one app and one site, and run your first small test this week. Grow from there. If you want more guides and templates, subscribe and tell me what you want to test next.