A firewall allows the organization to control traffic, reduce risk, and block threats.
If you manage networks or data, you already know pressure is high. I have helped teams roll out firewalls across offices, data centers, and cloud. I wrote this guide to show how a firewall allows the organization to act with confidence. You will learn what to block, what to allow, and how to avoid gaps. Stick with me, and you will see how to make a firewall work for you, not against you.
What a firewall allows the organization to do
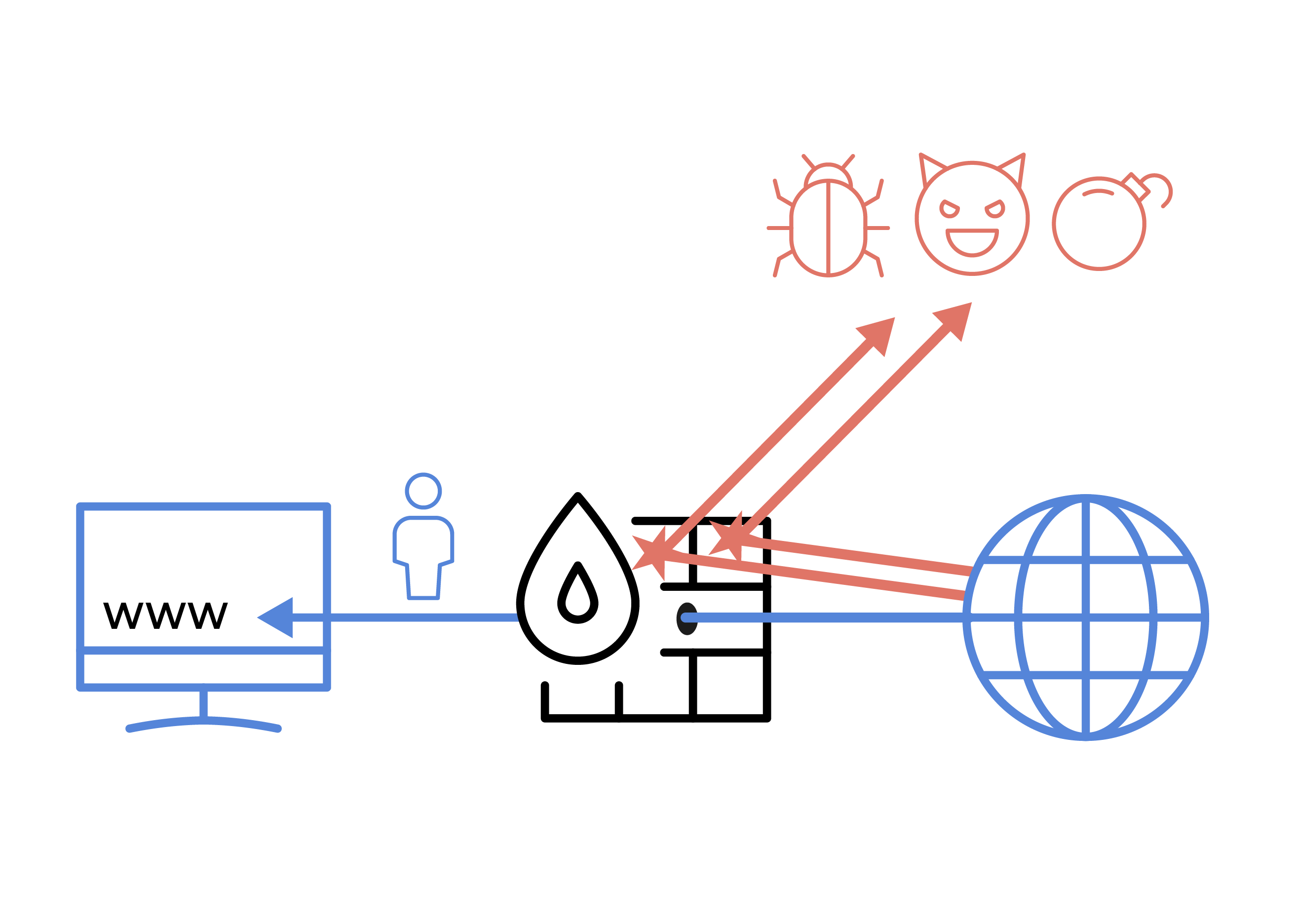
A firewall allows the organization to build guardrails for every connection. It sits at the edge or inside the network and filters traffic. It enforces policy so users and apps follow the rules. It turns broad risk into clear control.
A firewall allows the organization to reduce the attack surface. It can stop inbound scans and stop risky outbound calls. It maps users to traffic and tracks sessions. It also logs events for audits and learning.
A firewall allows the organization to do the following:
- Allow known business apps and block risky apps
- Enforce least privilege by port, user, device, and time
- Detect threats with intrusion prevention and DNS filtering
- Inspect encrypted traffic with care and consent
- Prove compliance with clear logs and reports

How modern firewalls work
Classic firewalls filter by IP, port, and protocol. Modern firewalls add state, user identity, and app awareness. They inspect packets, sessions, and content. They can match patterns that signal attacks.
Next-generation firewalls add intrusion prevention and sandboxing. They check domains and URLs against threat intel. They can decrypt and inspect TLS with set rules. They also learn from behavior over time.
A firewall allows the organization to mix these features with policy. It can treat finance traffic one way and guest traffic another. It can match cloud apps by name, not just port. It can block data leaks before they happen.
Types of firewalls and where they fit
A firewall allows the organization to pick the right tool for each layer. Each type fits a need and a place. Use more than one type for depth. Keep the design simple and clear.
Main types you will see:
- Network firewall for perimeter and internal segments
- Host firewall on servers and endpoints
- Web application firewall for HTTP and APIs
- Cloud firewall or security groups for cloud VPCs and VNets
- Firewall as a service in SASE or SSE platforms
- Industrial firewall for OT and ICS networks

Key benefits and use cases
A firewall allows the organization to enforce least privilege. It blocks bad by default and allows only what you need. It creates small blast zones so one breach does not spread. It keeps partners and vendors in safe lanes.
Common use cases:
- Secure remote work with VPN and MFA
- Protect web apps with a WAF and bot control
- Segment crown jewels from general users
- Stop malware callbacks with DNS and URL filtering
- Control shadow IT by app and user identity
A firewall allows the organization to show due care. It improves uptime by reducing noise. It turns vague risk into numbers that leaders can trust. It supports audits with clean, time-stamped logs.
Real-world stories and lessons learned
In one rollout, we cut an any-any rule at a remote site. We did it with a staged policy and a kill switch. Users saw no drop in key apps. Help desk tickets fell by half in a week.
In another case, TLS inspection broke a payroll site. We learned to add site-based bypass for some apps. We also shared a clear notice with users. Trust went up after that.
A firewall allows the organization to move fast with care. Test in monitor mode before you block. Keep a backout plan ready. Document each change in plain words.

Policy design and rule hygiene
Start with a deny-all baseline, then allow by need. Group objects by function, not by person. Use names that make sense to non-experts. Keep rules short and tested.
Good habits to keep:
- Review rules every quarter and recertify owners
- Remove stale rules after each project ends
- Log allow and deny for key apps and segments
- Use change windows and peer review for updates
- Track rule age, hits, and purpose in the ticket
A firewall allows the organization to turn policy into code. This needs care and rhythm. Small, steady updates beat big swings. Keep it clean so audits are easy.

Cloud, hybrid, and remote work
Cloud brings new paths and speeds. A firewall allows the organization to keep control across VPCs and VNets. Use cloud-native firewalls for east-west and egress. Add a WAF for apps and APIs at the edge.
Remote users need secure tunnels and strong auth. Tie the firewall to your identity provider. Limit access by user, device health, and app. This is a strong step toward zero trust.
SASE and SSE can help scale. They move controls closer to users and branch sites. They also cut backhaul and cost. Test with a pilot before a wide go-live.
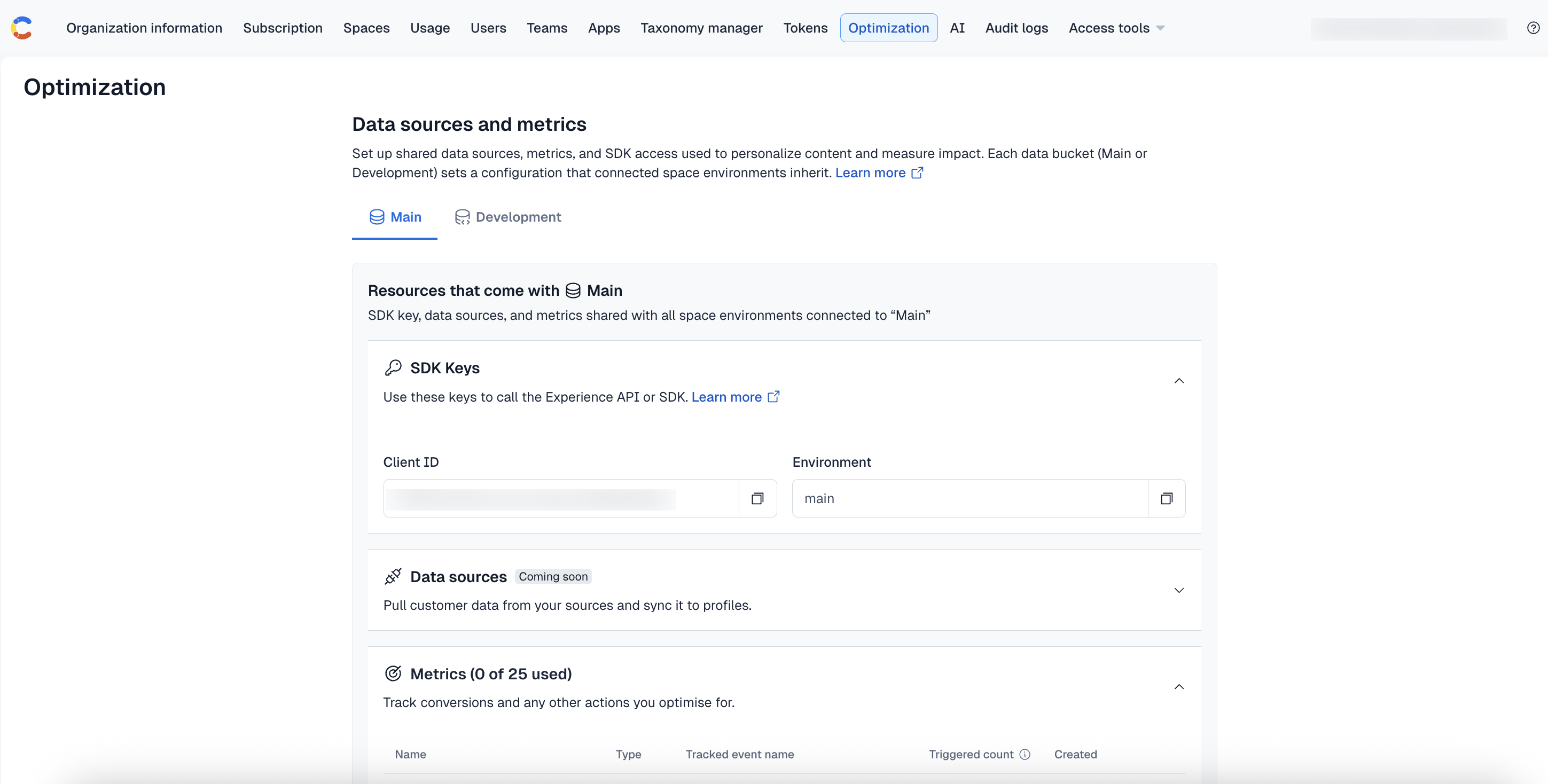
Measuring success and ROI
Leaders need proof, not promises. A firewall allows the organization to show value in numbers. Track what you block and what you allow. Tune so users stay fast and safe.
Useful metrics:
- Blocked high-risk events with context
- Mean time to detect and respond
- False positive rate and user impact
- Latency added for key apps
- Uptime of firewall clusters
- Audit findings resolved on time
Tie results to outcomes. Fewer incidents. Less dwell time. Better compliance. Clear logs when you need them.
Common mistakes to avoid
Do not leave any-any rules in place. They hide risk and mask gaps. Do not rely only on IP and port. Apps move and change.
Avoid blind spots with TLS traffic. Set clear rules for when to decrypt. Respect privacy and laws. Exclude health and banking sites.
A firewall allows the organization to cut noise. But do not turn on every feature at once. Start small, then grow. Keep configs in version control.
Step-by-step implementation roadmap
A firewall allows the organization to roll out change in steps. Work in small phases. Each step has a clear goal. Share updates with users and leaders.
- Define assets, data flows, and risk.
- Write simple policy statements in plain words.
- Design zones and choose firewall types.
- Build a lab and test core rules.
- Pilot with one site or app group.
- Migrate in waves with a backout plan.
- Enable advanced features and tune.
- Train ops, help desk, and users.
- Set up dashboards and alerts.
- Review metrics and improve monthly.
Integrating with the wider security stack
A firewall allows the organization to share context. Send logs to a SIEM for search and alerts. Use SOAR to automate common actions. Tie in EDR for host-level blocks.
Identity is key. Link users and groups to rules. Add NAC for device health checks. Use DLP and CASB for data-aware controls.
This stack can stop threats fast. It can also cut false alerts. One system boosts the next. The whole is stronger than the parts.
Compliance, governance, and audits
Many rules call for network controls. A firewall allows the organization to meet these needs. You can segment cardholder data. You can protect health data and logs.
Map rules to frameworks you follow. Keep reports on changes, reviews, and uptime. Store logs in a safe and write-once way. Make it easy for auditors to verify.
Good governance builds trust. It prevents drift. It also keeps teams aligned. Policy stays real, not paper-only.
Future trends to watch
Attackers hide in encrypted flows. Firewalls now use smarter methods to find bad in that space. QUIC and HTTP/3 bring new patterns. IPv6 use is also rising fast.
Edge sites need strong but light gear. OT and ICS need strict, simple rules. Zero trust network access is growing. AI will help with tuning and noise.
A firewall allows the organization to adapt fast. Keep firmware current. Test new features in a lab. Plan for change, not for stasis.
Frequently Asked Questions of a firewall allows the organization to
What does a firewall actually do day to day?
It checks each connection against rules and context. It allows known good traffic and blocks risky or unknown traffic.
Is a firewall enough to stop breaches?
No single tool is enough. A firewall works best with EDR, IAM, and good patching.
Do small businesses need next-generation firewalls?
Yes, if you use cloud, web apps, or remote work. Many NGFWs have simple modes that fit small teams.
Will TLS decryption slow my network?
It adds some load. Use hardware that fits your size and set smart bypass rules.
How often should we review firewall rules?
Do a light review each month and a deep review each quarter. Remove stale rules and confirm owners.
Can a firewall help with compliance?
Yes. It supports segmentation, logging, and access control. This maps to common audit needs.
What is the difference between a WAF and a network firewall?
A WAF protects web apps at the HTTP layer. A network firewall controls broader network flows across many protocols.
Conclusion
A firewall allows the organization to turn chaos into control. It limits risk, protects data, and keeps teams moving. With clear policy and clean rules, it becomes a steady ally.
Pick one small win to start this week. Review your top rules, log key events, and map one risky flow. If this helped, subscribe for more guides or leave a question so I can help next.