Business data networks connect systems and people; security protects data, uptime, and trust.
If you run a company today, your network is your business. This business data networks and security overview shows what to build, why it matters, and how to protect it. I have led network and security programs for years. I will give you deep, practical steps you can use now.

What Is a Business Data Network?
A business data network is the system that moves data between users, apps, and devices. It includes wires, Wi‑Fi, routers, switches, cloud links, and security tools. It keeps your team online and your data safe.
This business data networks and security overview explains how these parts fit. It shows what to secure first. It also helps you cut risk without slowing work.
Think of your network as roads and traffic lights. The roads move cars. The lights keep order. Security is the smart controller that stops crashes and blocks bad actors.

Why Security Matters
Security keeps three things strong. Confidentiality means only the right people see data. Integrity means no one changes data in secret. Availability means the network stays up.
The costs of a breach are high. There are fines, lost trust, and lost sales. Good controls lower risk and help you meet rules.
This business data networks and security overview links security to value. Strong networks speed work, pass audits, and protect brand equity.

Core Components of Modern Networks
Every network has core blocks that must be clear and secure.
- Endpoints include laptops, phones, and IoT devices.
- Network devices include routers, switches, and wireless access points.
- Edge and internet include firewalls, proxies, and DNS.
- Data centers and cloud host apps and databases.
- Identity and access control decide who gets in.
- Observability tools collect logs and metrics.
In this business data networks and security overview, these parts will show up often. Each one needs care and steady checks.

Common Network Architectures
Most firms use a mix of designs.
- LAN connects users in one site.
- WAN links sites over large areas.
- VPN secures remote users.
- SD‑WAN routes traffic by app needs and cost.
- Cloud networking links VPCs, VNets, and SaaS.
- Hybrid connects data center and cloud.
Pick what fits your size and risk. This business data networks and security overview covers trade‑offs, so you can choose with confidence.

The Security Stack
Security is a stack of layers that work together.
- Identity security uses SSO, MFA, and conditional access.
- Network security uses firewalls, segmentation, and DNS filtering.
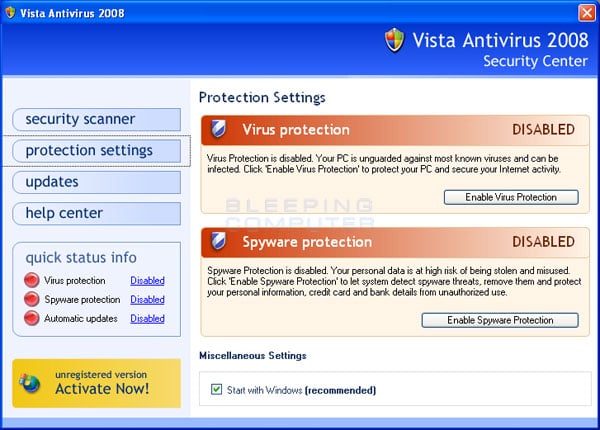
- Endpoint security uses EDR and device control.
- Data security uses DLP, encryption, and backup.
- App security uses secure coding, WAFs, and API gateways.
- Email and collaboration security stop phishing and data loss.
The business data networks and security overview you are reading ties these layers to the threats they stop.

Threat Landscape and Attack Paths
Most attacks start simple. A user clicks a phish. A device is unpatched. A key is exposed in code. Attackers then move sideways and seek admin rights.
Key threats to track:
- Phishing and business email compromise
- Ransomware and double extortion
- Insider risk and misuse of access
- Supply chain and third‑party exposure
- Cloud misconfigurations and public buckets
This business data networks and security overview stresses basics. Patch fast. Train users. Segment the network. These moves block many attacks.

Zero Trust for Business Data Networks
Zero Trust means never trust, always verify. Access depends on user, device, app, and context. It is simple on paper, hard in practice, and worth it.
Core steps:
- Verify identity with MFA and strong device checks.
- Limit access by least privilege and just‑in‑time rights.
- Segment networks and apps. Block broad lateral moves.
- Inspect traffic and logs. Respond in minutes, not days.
Treat this business data networks and security overview as your Zero Trust map. Start small. Expand fast. Measure often.

Governance, Risk, and Compliance
Good security rests on rules and proof. Use clear frameworks to guide work.
- Use NIST CSF or ISO 27001 to structure your program.
- Map controls to laws like GDPR, HIPAA, or PCI DSS.
- Classify data. Tie controls to data types and impact.
- Track third‑party risk with contracts and checks.
A mature business data networks and security overview links controls to real risks. It also shows auditors clear evidence.
Monitoring, Detection, and Incident Response
You cannot fix what you cannot see. Good visibility reduces dwell time and loss.
- Centralize logs in a SIEM. Cover identity, endpoints, network, and cloud.
- Use EDR or XDR for fast host detection.
- Add SOAR to automate routine triage and response.
- Write runbooks. Test them with tabletop drills.
- Keep backups offline and test restores.
This business data networks and security overview urges a 24x7 mindset. Alerts should be clear. Actions should be quick.
Designing a Secure Network: A Practical Blueprint
Here is a step‑by‑step path I use with teams.
-
Inventory and classify assets
Find users, apps, data, and third parties. Label sensitive data first. -
Build a reference architecture
Document LAN, WAN, cloud, and identity flows. Define trust zones. -
Segment and set controls
Use VLANs, firewalls, and micro‑segmentation. Restrict east‑west traffic. -
Harden and patch
Baseline configs. Remove defaults. Patch by risk. Track SLAs. -
Secure identity
Adopt SSO and MFA. Limit admin accounts. Rotate secrets. -
Encrypt everywhere
Use TLS for data in transit. Use strong keys for data at rest. -
Backup and recovery
Follow 3‑2‑1. Test restores monthly. Cover SaaS and cloud. -
Monitor and respond
Feed logs to SIEM. Tune rules. Drill the plan. -
Train and govern
Run phishing sims. Align to a framework. Report progress to leaders.
This business data networks and security overview becomes real when you follow a plan like this.
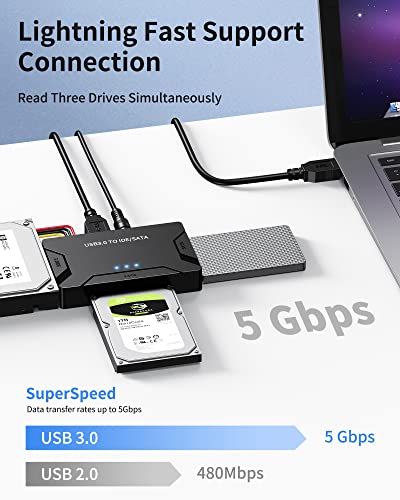
Tools and Technologies to Know
Choose tools that fit your size and skills. Buy fewer, better tools you can run well.
- Network: enterprise firewalls, SD‑WAN, DNS security, NAC
- Identity: SSO, MFA, PAM, passwordless options
- Endpoint: EDR, mobile management, device compliance
- Cloud: CSPM, CWPP, CIEM, secrets management
- Data: DLP, encryption key management, backup and DR
- Visibility: SIEM, NDR, XDR, SOAR
This business data networks and security overview is vendor neutral. Test tools in a pilot. Prove value before rollout.
Metrics, KPIs, and ROI
What gets measured improves. Keep metrics simple and tied to risk.
- Mean time to detect and respond
- Patch cycle times for critical fixes
- Phishing click rate and report rate
- Backup success rate and restore time
- Coverage of logs and assets
Use this business data networks and security overview to pick KPIs you can track each week. Share results with leaders in plain words.
Common Mistakes and How to Fix Them
I see the same traps again and again.
- Too many tools, not enough skill. Fix by reducing and focusing.
- Flat networks. Fix by segmenting and enforcing least privilege.
- Weak identity. Fix with MFA, SSO, and strong device health.
- Ignored backups. Fix with tests and clear recovery goals.
- Cloud drift. Fix with guardrails, policies, and IaC.
A solid business data networks and security overview helps you spot these early and act fast.
Real‑World Lessons From the Field
A mid‑size firm called me after a ransomware scare. Email rules were weak. Backups had not been tested. We set MFA, tightened mail filters, segmented the file shares, and tested restores. Two months later, a phish hit, but impact was near zero.
At a global startup, costs ballooned from tool sprawl. We ran a hard review. We cut three tools, kept two, and tuned alerts. The team went from burnout to control. This business data networks and security overview works when you keep it simple and stick to basics.
Future Trends to Watch
The network is moving to the edge. Users and data are everywhere. Controls must follow.
- SASE and SSE merge network and security in the cloud.
- Passwordless and passkeys reduce phishing risk.
- AI speeds both attack and defense. Use it with care.
- Post‑quantum crypto planning starts now for long‑lived data.
- 5G, OT, and IoT widen the attack surface.
Keep this business data networks and security overview close as these trends mature. Update your plan each quarter.
Frequently Asked Questions of business data networks and security overview
What is the fastest way to improve network security?
Enable MFA for all users and admins. Then patch internet‑facing systems and review backups.
How often should we test incident response?
Run a tabletop drill each quarter. After each drill, update runbooks and fix gaps.
Do small businesses need Zero Trust?
Yes, in a simple form. Start with MFA, device checks, and basic segmentation.
How do we secure remote work?
Use SSO, MFA, device compliance, and a modern VPN or ZTNA. Log access and enforce least privilege.
What is the best first metric to track?
Track mean time to patch critical issues. It shows speed and reduces real risk.
How do we secure cloud networks?
Use strong identity, native security controls, and guardrails in IaC. Monitor with CSPM and fix drift fast.
Are email filters enough to stop phishing?
No. Use filters plus MFA, user training, and tight admin controls. Assume some phish will get through.
Conclusion
Your network is your business engine. Protect it with clear design, strong identity, smart segmentation, steady patching, and fast response. This business data networks and security overview gives you the blueprint to start today.
Pick one step this week. Turn on MFA, segment one zone, or test a restore. Small wins stack up fast. Want more guidance like this? Subscribe, share your questions, or ask for a walkthrough of your current setup.