Verify stability, security, performance, data integrity, documentation, and user acceptance before sign-off.
You just changed your system. Now do not guess. Use a proven checklist after completing system reconfiguration to confirm things are safe and fast. I have led reconfig efforts in high-stakes teams for years. This guide shows what to check, why it matters, and how to prove it with evidence. Follow it to reduce risk and gain clean, audit-ready sign-off.
Post-Change Verification Essentials
A checklist after completing system reconfiguration should start with basic health checks. Confirm the change scope. Make sure every service starts and stays up. Check key paths end to end. This prevents hidden failures.
Do these right away:
- Confirm the version, build, and config state match the plan.
- Validate service status and ports. Check dependencies like DNS, NTP, message queues, and databases.
- Run smoke tests on top user flows. Note the result and time.
- Compare current health to the baseline from before the change.
- Review logs for errors, warnings, and timeouts.
From my experience, a two-minute smoke test can save a two-day outage. Keep the checklist after completing system reconfiguration close and use it line by line.

Security and Compliance Checks
Security is not an afterthought. A checklist after completing system reconfiguration must include hardening and audit checks. Small gaps here become big risks later.
Validate these items:
- Apply least privilege on services, keys, and secrets.
- Check firewall rules, security groups, and routing. Confirm expected ingress and egress only.
- Confirm patch level and scan for known issues.
- Ensure TLS versions, cipher suites, and cert chains are correct and current.
- Verify logging to a secure store. Include audit trails for admin actions.
Map checks to well known controls such as CIS, NIST SP 800-53, and ISO 27001. Document proof right in the checklist after completing system reconfiguration.
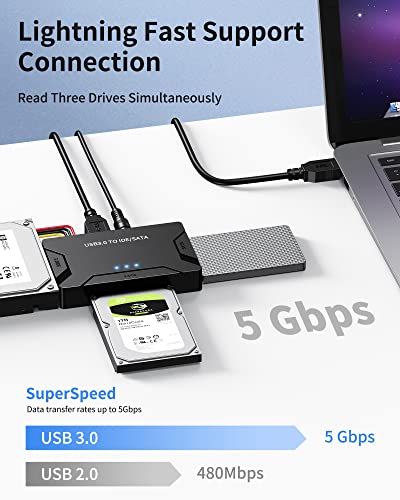
Performance and Capacity Validation
Speed is part of trust. After a change, workloads can shift. Your checklist after completing system reconfiguration should verify performance and headroom.
Check these signals:
- CPU, memory, disk IOPS, and network latency against pre-change baselines.
- App latency, throughput, error rate, and saturation.
- Garbage collection, thread pools, and connection pools.
- Queue depth, cache hit rate, and database locks.
- A small load test to ensure stability under stress.
Keep a target like 30 percent headroom for peak load. Note results in the checklist after completing system reconfiguration.
Data Integrity and Backup Assurance
The fastest system is useless if data is wrong. This part of the checklist after completing system reconfiguration protects your data and your job.
Do the following:
- Verify database health, replication lag, and integrity checks.
- Confirm backup jobs ran before the change and after the change.
- Perform a small restore test to a safe sandbox.
- Check schema drift. Ensure migrations match the plan.
- Validate file integrity where configs or binaries changed.
I once saw a team skip a quick restore test. Days later, they found broken backups. A two-minute restore check would have saved them. Add that step to your checklist after completing system reconfiguration.

Documentation and Knowledge Transfer
If it is not written, it did not happen. A strong checklist after completing system reconfiguration includes docs and handoffs.
Include these tasks:
- Update the CMDB, diagrams, and runbooks.
- Record new IPs, ports, versions, and feature flags.
- Capture screenshots of key dashboards and test results.
- Summarize the change in plain words for support teams.
- Store the evidence with the change record.
This reduces hero work at 2 a.m. and supports audits. It also keeps the checklist after completing system reconfiguration useful for the next change.
User Acceptance and Business Validation
Tech checks are not enough. The business must confirm value. Your checklist after completing system reconfiguration should include user sign-off.
Cover the following:
- Ask a product owner or SME to run top journeys.
- Validate SLAs and key KPIs like conversion or task time.
- Confirm emails, files, and reports arrive as expected.
- Gather a short sign-off note with time and name.
I always schedule a 10-minute UAT window. This single step made go-live calls calm. Make it part of the checklist after completing system reconfiguration.

Monitoring, Alerting, and Observability
What you cannot see, you cannot fix. Embed observability in the checklist after completing system reconfiguration.
Verify:
- Dashboards for system and app health show sane values.
- Alerts exist for error rate, latency, saturation, and queue depth.
- Synthetic checks for public endpoints and key flows run every minute.
- Log shipping, trace sampling, and metrics labels work.
- SLOs and SLIs are clear and tracked.
Good alerts should be rare and loud. Bad alerts are common and quiet. Tune them now with the checklist after completing system reconfiguration.

Rollback Readiness and Disaster Recovery
Even a clean change can fail later. A smart checklist after completing system reconfiguration keeps rollback fast and DR ready.
Confirm these points:
- Rollback steps are still valid after the change.
- Snapshots, AMIs, or images exist and are accessible.
- Database restore points meet RPO and RTO goals.
- DR runbooks are updated and tested on a schedule.
- Feature flags can disable new paths quickly.
Practice rollback in a safe lab. Time it. Record the result in the checklist after completing system reconfiguration.
Governance, Change Records, and Audits
Auditors love proof. Future you will too. A thorough checklist after completing system reconfiguration creates a strong paper trail.
Include:
- Link CAB approval, impact analysis, and risk rating.
- Attach test plans, logs, and screenshots.
- Note who did what and when.
- Tag code commits and config changes with the ticket ID.
- Close tasks only when evidence is attached.
Align with ITIL and internal policies. Keep the checklist after completing system reconfiguration as the one source of truth.
Common Pitfalls and How to Avoid Them
Avoid these traps with your checklist after completing system reconfiguration.
Watch for:
- No baseline. Always collect pre-change metrics and logs.
- DNS and cache delays. Lower TTLs before changes and clear caches.
- Clock drift. Sync time or auth and logs will break.
- Secret scopes. Least privilege can block new paths. Test tokens.
- Hidden dependencies. Map external APIs, storage, and queues.
Each pitfall is easy to miss when tired. A simple list keeps you safe. That is why the checklist after completing system reconfiguration matters so much.
Sample 30-Minute Post-Reconfig Runbook
Use this quick runbook as part of your checklist after completing system reconfiguration. It is short and sharp.
- Minute 0 to 3. Confirm versions, services, ports, and dependency health.
- Minute 3 to 8. Run smoke tests on top user flows. Capture screenshots.
- Minute 8 to 12. Check logs and errors. Compare to baseline.
- Minute 12 to 18. Review security rules and secrets. Verify TLS and access.
- Minute 18 to 23. Check performance metrics and headroom. Run a light load.
- Minute 23 to 27. Confirm backups, replication, and run a small restore test.
- Minute 27 to 30. Update the ticket, attach evidence, and gather UAT sign-off.
Add or remove steps to match your stack. Keep it in the checklist after completing system reconfiguration and repeat every time.
Frequently Asked Questions of checklist after completing system reconfiguration
What is the main goal of a checklist after completing system reconfiguration?
It proves the system is stable, secure, and ready for users. It also creates evidence for audits and future reviews.
How long should the checklist after completing system reconfiguration take?
Most checks fit in 30 to 60 minutes. Complex systems or strict rules may need more time and deeper tests.
Who should sign off on the checklist after completing system reconfiguration?
The technical owner and a business owner should sign. This ensures both system health and business value are confirmed.
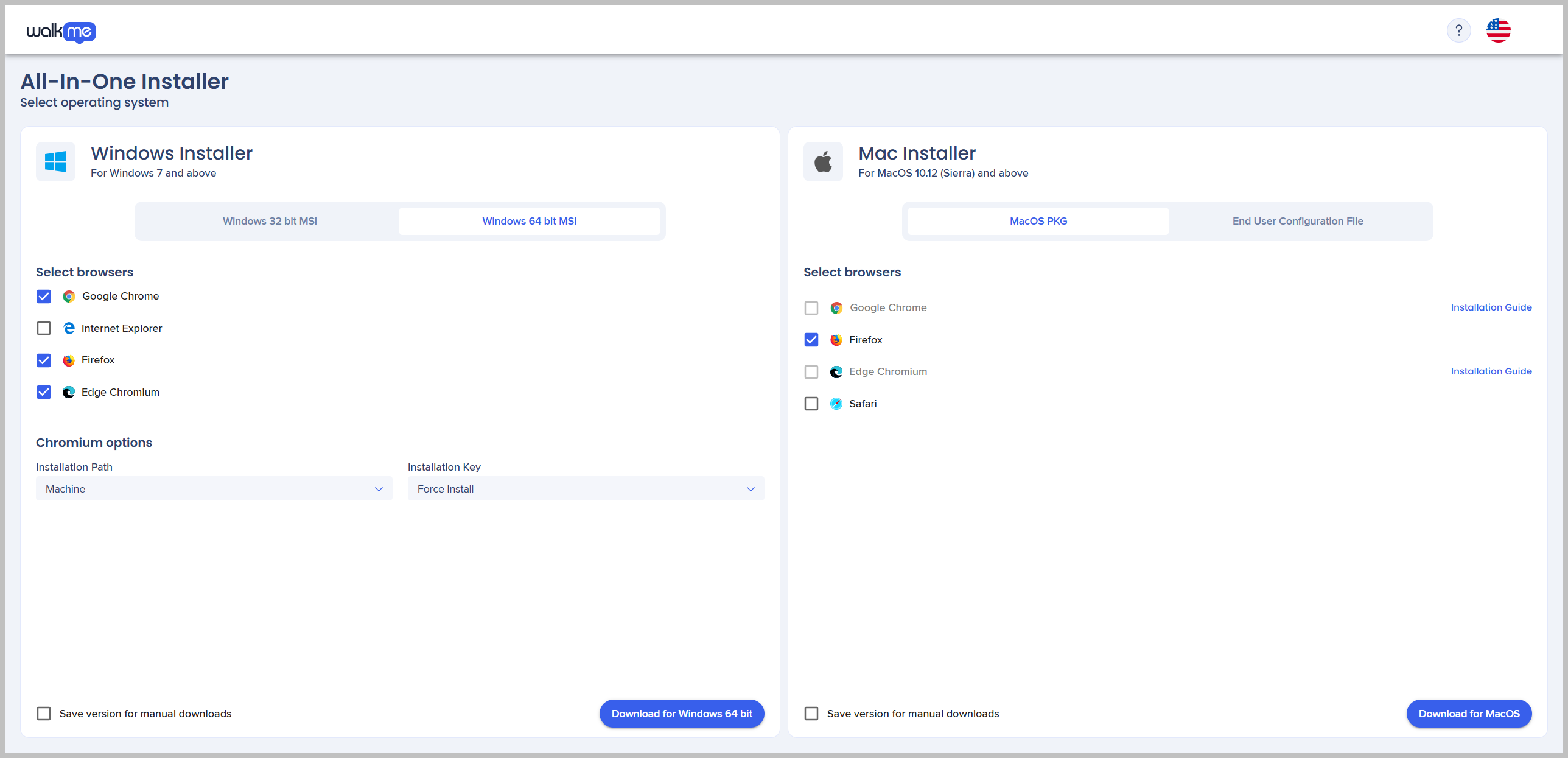
What tools help with the checklist after completing system reconfiguration?
Use monitoring dashboards, log search, config management, and APM tools. Synthetic checks and backup tools also help a lot.
How often should I update my checklist after completing system reconfiguration?
Review it after every major change and every quarter. Add new risks, retire old steps, and adjust to new controls.
What if a step fails during the checklist after completing system reconfiguration?
Pause and assess impact. Roll back if user harm is likely or if core controls fail.
Conclusion
A strong checklist after completing system reconfiguration turns risk into routine. It confirms health, secures data, and builds trust with solid proof. It also saves time in audits and during tense calls.
Start with the runbook above. Tune it to your stack. Use it after every change. Then share the wins with your team. Ready to go deeper? Subscribe for more guides, templates, and field-tested checklists.