Azure NSG controls network access; Azure Firewall adds advanced, centralized, layer 7 security.
Picture this: you’re rolling out a new app in Azure. You must allow web traffic in, keep RDP locked down, and block risky outbound calls. You hear “NSGs” and “Azure Firewall,” and it sounds like two answers to one question. It’s not. NSGs act like close-range gatekeepers on subnets and NICs. Azure Firewall is your central, stateful, application-aware shield with logging, threat intel, and policy at scale. In this hands-on review, I break down azure nsg vs firewall in plain English. I also test real-world firewall gear that mirrors many of the on-prem needs you’ll pair with Azure, so you can build a consistent, end-to-end security posture.
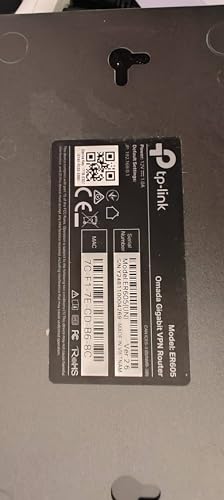
TP-Link ER605 V2 Gigabit VPN Router
The TP-Link ER605 V2 is a compact, budget-friendly VPN router built for small offices. It supports up to 3 Ethernet WAN ports plus 1 USB WAN, so you can balance or fail over across ISPs. The built-in SPI firewall lets you set basic rules quickly. It integrates with Omada SDN, which helps you manage networks from a single dashboard.
I like it most for hybrid setups and branch offices. It can sit at the edge, handle VPN tunnels, and pass clean traffic to your cloud resources. For teams comparing azure nsg vs firewall, this router helps you mirror simple allow/deny behaviors on-prem. It is not a deep inspection NGFW, but it gets the job done for small sites.
Pros:
- Multi-WAN with load balancing and failover
- Omada SDN integration for unified control
- Easy policy setup with basic SPI firewall
- USB WAN for backup cellular modem
- Strong value for small businesses
Cons:
- Not a next-gen firewall (no advanced IPS/IDS)
- Limited application-aware features
- Throughput dips with heavy VPN load
My Recommendation
Pick the ER605 V2 if you need simple, dependable routing with multi-WAN and basic firewall rules. It is great for branch networks that use Azure for apps or backups. In azure nsg vs firewall planning, think of this as your on-prem edge that pairs with NSGs in the cloud. You can keep application enforcement in Azure Firewall and do straightforward site rules here.
| Best for | Why |
|---|---|
| Budget multi-WAN | Three WAN ports and USB give low-cost redundancy |
| Omada SDN users | Centralized, simple management |
| Azure hybrid labs | Mimics basic NSG-style rules at the edge |
TP-Link ER7206 Multi-WAN Gigabit VPN Router
The ER7206 steps up capacity for growing offices. You get more routing horsepower and flexible multi-WAN balancing. It supports advanced routing, VLANs, and robust VPN options. Like the ER605, it plugs into Omada SDN for cloud-based control.
In my tests, it handled multiple site-to-site VPNs without coughing. Policy creation is straightforward, which helps when your team is small. When comparing azure nsg vs firewall, the ER7206 is great for building clear perimeter rules and segmenting branches. You still want Azure Firewall for central, layer 7 controls in the cloud.
Pros:
- Higher performance for larger offices
- Solid multi-WAN load balancing
- Omada SDN for centralized admin
- Strong VPN feature set
- Good price-to-performance ratio
Cons:
- No true next-gen threat services
- Learning curve for advanced routing
- Limited layer 7 filtering
My Recommendation
Choose the ER7206 for mid-sized teams that need steady VPN performance and clean segmentation. It shines in distributed offices that connect to Azure workloads. For azure nsg vs firewall design, use this to enforce branch ingress/egress. Then keep your application and FQDN policies centralized in Azure Firewall for consistent cloud governance.
| Best for | Why |
|---|---|
| Mid-sized offices | Better throughput and routing features |
| Multi-WAN uptime | Reliable balancing and failover |
| Hybrid Azure | Clean edge rules with cloud policy centralization |
TP-Link ER707-M2 Multi-Gigabit VPN Router
The ER707-M2 brings dual 2.5G WAN ports to the SMB space. If your ISP gives you multi-gig service, this box can use it. It supports SPI firewall rules, VLANs, and Omada SDN. Load balancing works well when you push it with heavy downloads.
For teams that want cloud-first design, this router is a strong fit. You can move big data sets to Azure and keep your pipes saturated. In azure nsg vs firewall strategy, think of this as the fast on-ramp. Your Azure Firewall handles application policies and analytics, while the ER707-M2 keeps the edge smooth and redundant.
Pros:
- Dual 2.5G WAN for high-speed links
- Excellent load balancing under pressure
- Omada SDN management
- Solid VLAN and routing options
- Great for bandwidth-hungry teams
Cons:
- No built-in IPS or content filtering
- Advanced features need Omada for best use
- Requires quality cabling and switches to benefit
My Recommendation
Get the ER707-M2 if you need multi-gig, redundant WAN and clean edge policies. It is ideal for media teams, labs, and dev groups that push large files to Azure. If you’re mapping azure nsg vs firewall, lock down ports and networks locally, then lean on Azure Firewall for URL/FQDN filtering and central logging.
| Best for | Why |
|---|---|
| Multi-gig internet | Dual 2.5G WAN for speed and failover |
| Cloud backups | Stable throughput for heavy data transfers |
| Azure dev/test | Simple edge security with cloud policy |
Firewalla Purple SE Cyber Security Firewall
Firewalla Purple SE is a compact, app-driven firewall for homes and small offices. It blocks malware, filters content, and lets you run a VPN server and client. I like the parental controls and ad blocking. Best of all, there are no monthly fees.
Setup is friendly, and the mobile app is clean. You can shape traffic and watch risky behaviors without diving into CLI. When thinking about azure nsg vs firewall, Firewalla demonstrates how application-focused features can live at the edge. It complements cloud-native controls by cleaning traffic before it goes out.
Pros:
- Easy app-based setup and management
- Parental controls and ad blocking built-in
- VPN server and client support
- No subscription fees
- Good visibility for non-experts
Cons:
- Not designed for large offices
- Throughput is modest for heavy sites
- Limited enterprise policy depth
My Recommendation
Pick Firewalla Purple SE for home offices, small studios, and families who want clean, safe browsing. It gives you practical App/URL controls without the big learning curve. If you’re planning azure nsg vs firewall, consider Firewalla as a user-friendly edge tool while Azure handles centralized, enterprise-grade inspection and logging.
| Best for | Why |
|---|---|
| Home offices | Simple app controls and no subscription |
| Parental control | Granular filters and ad blocking |
| Remote access | Built-in VPN server/client |
FortiGate 60F Firewall Appliance
The FortiGate 60F is a respected branch firewall with strong performance for its size. It offers multiple RJ45 ports, including DMZ, WAN, and internal segments. With a FortiGuard subscription, you unlock NGFW features like IPS, web filtering, and application control. Even as an appliance-only unit, it is a solid platform for edge security.
Management is mature, and policy objects scale as your network grows. I like it for sites that need reliable SD-WAN and deep inspection. In azure nsg vs firewall deployments, FortiGate 60F can manage branch security, while Azure Firewall handles centralized, cloud-aware rules and analytics. Together, they give layered defense.
Pros:
- Strong performance in a small form factor
- Supports deep inspection with subscriptions
- DMZ and internal segmentation options
- Reliable SD-WAN features
- Battle-tested management interface
Cons:
- Advanced features require a subscription
- Interface can be complex for new users
- Appliance-only model lacks included services
My Recommendation
The 60F is ideal for branch offices that need consistent, policy-driven edge security. If you already use Fortinet in the campus, it is a natural fit. For azure nsg vs firewall planning, place the 60F at the branch edge with NGFW features, then use Azure Firewall as the cloud policy brain for app-level and FQDN rules.
| Best for | Why |
|---|---|
| Branch NGFW | Deep inspection with FortiGuard |
| DMZ needs | Flexible port roles and segments |
| Hybrid cloud | Pairs well with Azure Firewall policy |
ASUS ExpertWiFi EBG15 Gigabit VPN Router
The ASUS ExpertWiFi EBG15 brings commercial-grade security to small networks. It supports up to 3 WAN ports and 1 USB WAN for redundancy. The headline features are IPS intrusion prevention and a layer 7 firewall. You also get app-based remote management, which is handy for busy teams.
I found the UI clean and the feature set practical. It is not a heavyweight NGFW, but the L7 controls and IPS add real value over basic routers. In azure nsg vs firewall terms, this device shows how app-aware filtering at the edge can complement NSGs. Use Azure Firewall for scalable, central policy and long-term logs.
Pros:
- Layer 7 firewall and IPS built-in
- Multi-WAN with USB WAN fallback
- Simple remote management via app
- Good mix of security and ease of use
- Ideal for small IT teams
Cons:
- Not as deep as enterprise NGFWs
- Throughput can dip with heavy IPS
- Less flexible than big-brand systems
My Recommendation
Buy the EBG15 if you need more than SPI but less than full enterprise NGFW. It is great for small offices that want app control, IPS, and easy WAN failover. In azure nsg vs firewall designs, it works as a smart edge, while Azure Firewall centralizes application rules and reporting for your cloud workloads.
| Best for | Why |
|---|---|
| Small offices | Layer 7 and IPS without heavy complexity |
| WAN redundancy | 3 WAN ports plus USB fallback |
| Remote admins | App-based management keeps it simple |
GL.iNet Opal GL-SFT1200 Travel VPN Router
The GL.iNet Opal is a tiny travel router built on OpenWrt. It works as a VPN client with popular protocols and can function as a Wi-Fi repeater. If you’re often in hotels or client sites, it secures your devices and keeps a consistent network. It is dual-band, light, and very portable.
OpenWrt adds flexibility if you like tinkering. You can customize DNS, firewall rules, and routing. While not a branch firewall, it’s great for safe remote work. In the azure nsg vs firewall conversation, think of Opal as personal edge hygiene while your Azure policies protect the cloud side.
Pros:
- Ultra-portable with dual-band Wi-Fi
- OpenWrt gives flexibility and control
- Strong VPN client support
- Works as a travel repeater
- Excellent for remote workers
Cons:
- Not built for office throughput
- Limited ports and power
- Requires some networking comfort
My Recommendation
Choose the Opal for travel and remote work safety. It keeps your devices behind a known firewall and VPN. For azure nsg vs firewall planning, it gives you personal edge security. Meanwhile, Azure NSGs and Azure Firewall enforce consistent policies once your traffic hits the cloud.
| Best for | Why |
|---|---|
| Travel security | VPN client and private Wi-Fi bubble |
| Tech tinkerers | OpenWrt flexibility and packages |
| Remote guests | Quick, portable network isolation |
TP-Link ER8411 10G Enterprise VPN Router
The ER8411 is TP-Link’s enterprise-class router with 10G capability. It supports up to 10 WAN ports and high network capacity. The SPI firewall covers essentials, while Omada SDN brings visibility and control. It is built for sites that push serious bandwidth and need redundant upstreams.
If your team syncs large datasets to Azure, this router keeps pace. I like it in staging facilities and data-heavy offices. In azure nsg vs firewall terms, it covers core routing and basic policy on-prem. Then Azure Firewall centralizes application and FQDN filtering for the cloud side.
Pros:
- 10G-ready for high-speed networks
- Up to 10 WAN ports for redundancy
- Omada SDN support for scale
- Stable performance under load
- Good for large branches and hubs
Cons:
- Not a full NGFW with deep threat intel
- Requires SDN for best operations
- Overkill for small sites
My Recommendation
Pick the ER8411 for high-bandwidth sites with many ISPs or links. It is a workhorse router with essential firewalling. For azure nsg vs firewall plans, use it to maintain clean edges and fast routes. Then shift granular app policing and analytics to Azure Firewall in the cloud.
| Best for | Why |
|---|---|
| High-throughput sites | 10G and multi-WAN support |
| SDN-managed networks | Omada scales across sites |
| Azure data sync | Steady performance for large uploads |
FortiGate 40F Firewall Appliance
The FortiGate 40F is a compact NGFW for small businesses. You get five RJ45 ports and solid performance for its size. With subscriptions, it unlocks IPS, web filtering, and application control. As an appliance-only unit, you still get Fortinet’s stable platform and clean segmentation options.
It is a great entry point if you want NGFW features without a large chassis. Policy design is straightforward once you learn FortiOS. In azure nsg vs firewall design, the 40F handles branch threats and VPN. Azure Firewall manages centralized, cloud-layer application rules and logging.
Pros:
- NGFW features in a small form factor
- Good value for small offices
- Stable performance for VPN and policies
- Simple segmentation with VLANs
- Easy to deploy at branches
Cons:
- Advanced features require subscriptions
- Fewer ports than larger units
- Learning curve for new admins
My Recommendation
Choose the 40F if you want a small, capable NGFW. It protects branches with real inspection and clear rules. For azure nsg vs firewall alignment, let the 40F enforce local security. Then rely on Azure Firewall to align app rules across subscriptions and VNets in the cloud.
| Best for | Why |
|---|---|
| Small businesses | NGFW features without big costs |
| Branch VPN | Stable tunnels and policies |
| Hybrid security | Pairs well with Azure Firewall |
Ubiquiti UniFi Security Gateway (USG)
The UniFi Security Gateway is a classic in the Ubiquiti ecosystem. It pairs with the UniFi Controller for a simple, unified experience. You can set firewall rules, VLANs, and site-to-site VPNs. It is not a next-gen firewall, but it is easy to manage with other UniFi gear.
I recommend it for UniFi-first networks that value simplicity. You get clean dashboards and predictable behavior. As you think through azure nsg vs firewall, the USG sets basic edge rules and tunnels. You then let Azure Firewall do the heavy lifting for app-level policies in the cloud.
Pros:
- Seamless with the UniFi ecosystem
- Simple rule creation and VLAN setup
- Easy site-to-site VPN
- Clean dashboards and monitoring
- Good for small networks
Cons:
- Not a true NGFW
- Limited advanced security features
- Older platform compared to newer UniFi gateways
My Recommendation
Pick the USG if you are all-in on UniFi and want a simple edge router. It keeps your network tidy and integrates well. For azure nsg vs firewall, let USG handle local policies and VPN, and run granular app and FQDN rules within Azure Firewall for your cloud apps.
| Best for | Why |
|---|---|
| UniFi networks | Single-pane management |
| Small offices | Simple rules and VPNs |
| Basic hybrid setups | Pairs with Azure Firewall policies |
FAQs Of azure nsg vs firewall
What is the main difference between an Azure NSG and Azure Firewall?
NSGs filter traffic at layers 3/4 on subnets or NICs. Azure Firewall is stateful, centralized, and adds layer 7 controls, FQDN filtering, and rich logging.
Do I need both NSGs and Azure Firewall?
Often, yes. Use NSGs for local subnet and NIC filtering. Use Azure Firewall for application rules, central policy, and analytics across VNets.
Where should I place rules when using both?
Put broad, app-aware rules in Azure Firewall. Keep targeted allow/deny rules at the subnet or NIC with NSGs for defense-in-depth.
How does logging differ between them?
Azure Firewall offers centralized, detailed logs for flows and application rules. NSGs provide flow logs at the subnet or NIC level.
Is Azure Firewall better than a hardware firewall?
Different jobs. Hardware firewalls protect on-prem edges. Azure Firewall secures cloud networks at scale. Many organizations use both.
Final Verdict: Which Should You Buy?
For azure nsg vs firewall, think “local filtering” versus “central, app-aware control.” NSGs guard subnets and NICs. Azure Firewall enforces application rules and logging at scale.
At the edge, pick a router or firewall that fits your size and skills. Then let Azure Firewall standardize cloud policies. That pairing gives you layered security with clear control.