Review code with tools and people to catch risks early and fix them fast.
If you want to know how to audit source code the right way, you are in the right place. I have led secure code reviews for startups and large teams. I will show you how to audit source code with a clear plan, simple steps, and real examples. You will learn what to check, which tools to use, and how to turn results into action.
What Is a Source Code Audit?
A source code audit is a deep review of code. It looks for security bugs, logic flaws, and weak patterns. It uses both tools and manual review. It ends with a report, fixes, and proof that the fixes work.
This guide explains how to audit source code for both web and native apps. We will cover scope, tools, checklists, and workflow. You will see how to make it part of your build and release process.
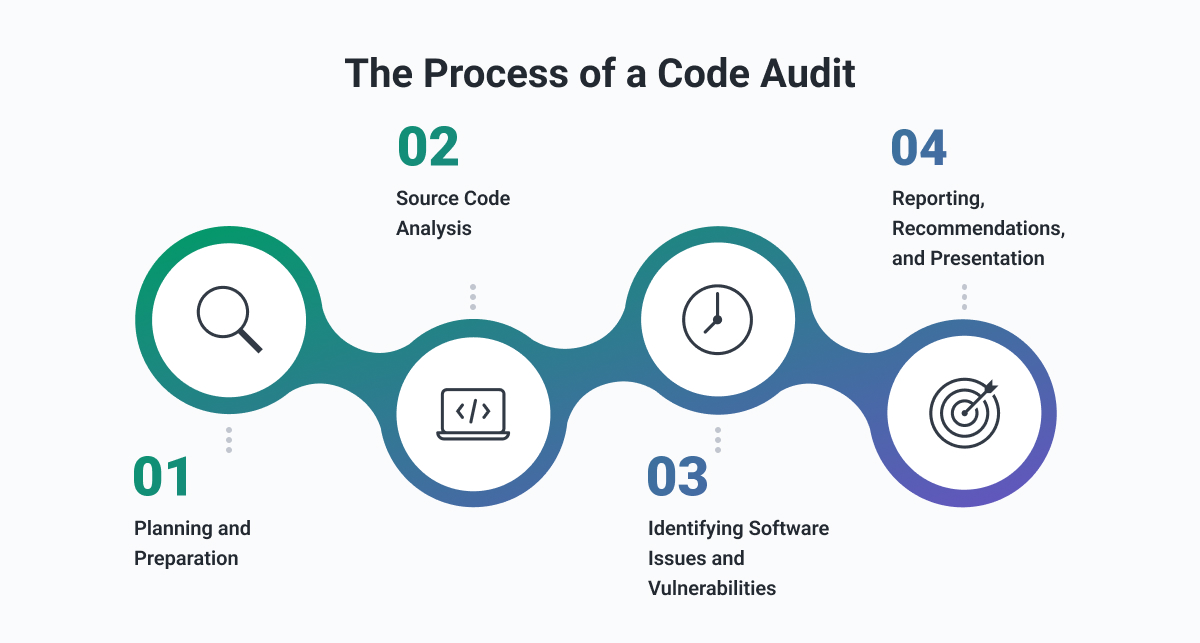
A Simple 8-Step Plan for how to audit source code
Here is how to audit source code in eight clear steps. Use it for any stack. Keep each step small and repeat often.
- Define scope and goals
- Set up tools and baselines
- Run automated scans
- Review results and filter noise
- Do focused manual review
- Re-test with targeted cases
- Report risks and fixes
- Verify fixes and track metrics
As you learn how to audit source code, start small. Audit one service first. Build a playbook. Then scale.
Set Up: Scope, Risk, and Rules
Good audits start with scope. Pick repos, branches, and time. Map your threat model. Note data types, auth paths, and third-party code.
Define rules for risk rating. Use impact and chance. Mark what needs proof. Agree on timelines. Decide what to fix now and what to log.
Write down how to audit source code for your team. Keep it short. Add owners, tools, and handoffs.

Automated Scans That Work
Automated checks catch fast wins. They also set a baseline trend. Use a small set of tools that fit your stack.
Use:
- SAST to scan code for common flaws
- SCA to check libraries and licenses
- Secret scanners to catch keys and tokens
- Linters to enforce safe patterns
- IaC scanners for cloud configs
Tune rules. Suppress false hits at the source. Run on every pull request. This is core to how to audit source code at scale.

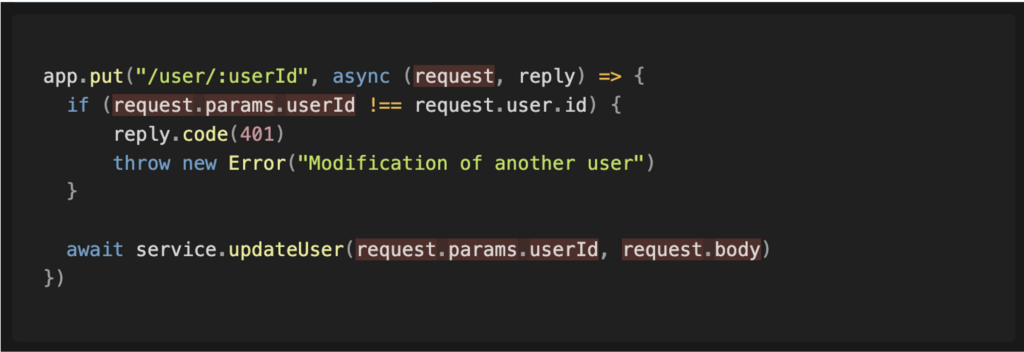
Manual Review: Finding Flaws Humans Catch
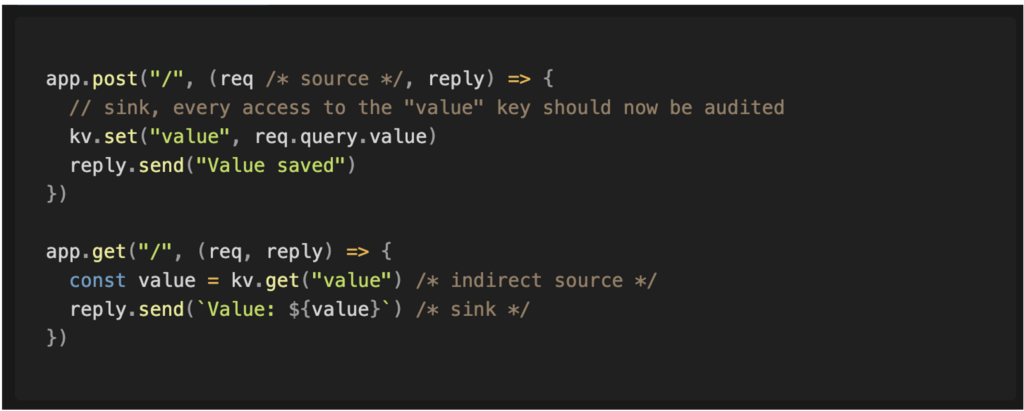
Tools miss logic bugs. Manual review finds them. Focus on code that moves or guards data. Trace flows through auth, input, and storage.
Use a checklist. Read code in small parts. Ask what can go wrong. Pair on tricky spots. When I audit auth code, I write small tests to confirm each branch.
Document what you see. Note risky patterns. This is the heart of how to audit source code with care.

Deep Dives: Auth, Crypto, and Data Flows
Some areas need extra time. They hold the most risk.
Focus on:
- Authentication and session logic
- Authorization checks on each action
- Input validation and output encoding
- Crypto use, key storage, and random numbers
- File handling and path joins
- Deserialization and reflection
- Query building and ORM usage
- Error handling and logs
When learning how to audit source code, trace data from user to sink. Look for trust jumps. Look for missing checks.
Secure Coding Checks by Language
Each language has traps. Here are quick checks I use often.
JavaScript and TypeScript:
- Avoid eval and new Function
- Escape HTML; use vetted template engines
- Validate JSON and query inputs
Python:
- Avoid pickle for untrusted data
- Use parameterized queries
- Watch for wide except blocks
Java and Kotlin:
- Use prepared statements
- Enforce null checks and input limits
- Use secure random and crypto suites
C and C++:
- Prefer safe string functions
- Watch for integer overflow
- Use bounds checks and static analyzers
Use these as you decide how to audit source code in your stack.

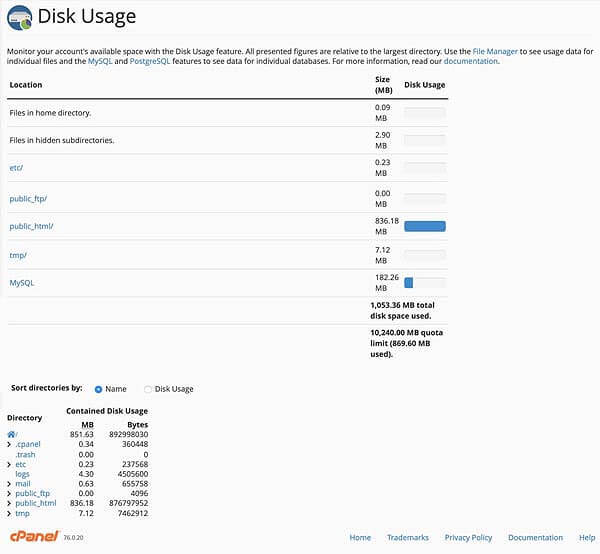
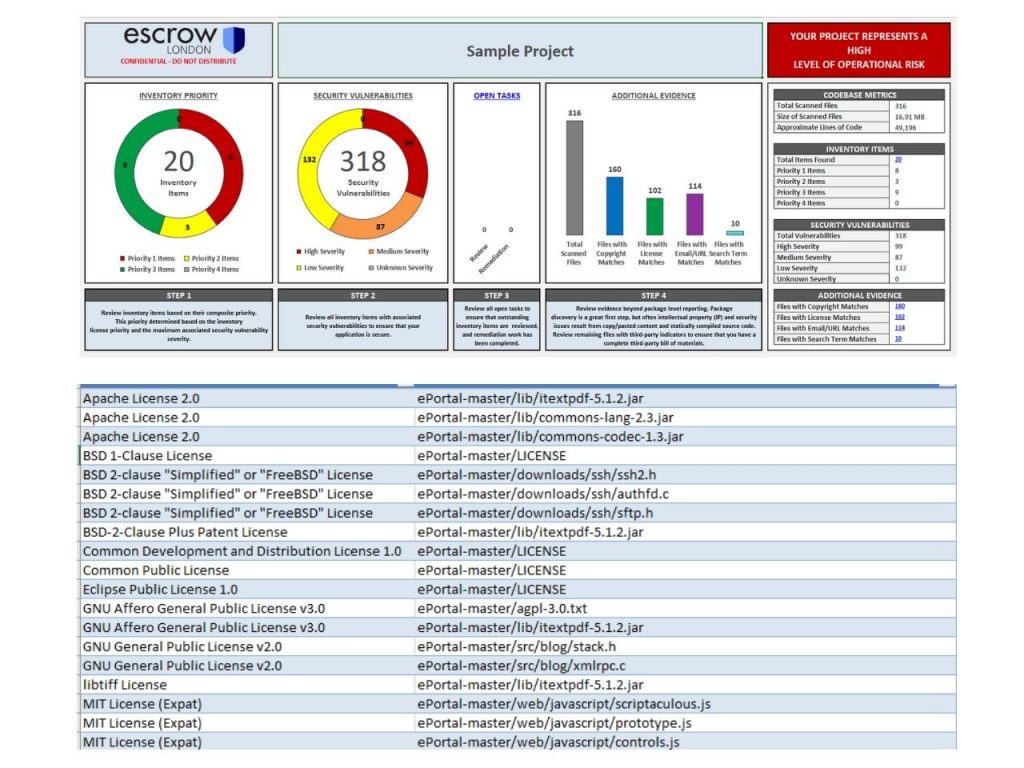
Metrics, Reports, and Risk Ranking
Good audits produce clear reports. They guide what to fix first. Keep it short and visual.
Include:
- Summary of scope and findings
- Risk table with severity, impact, and evidence
- Proof of concept or test links
- Fix guidance per issue
- Trend charts across sprints
Set targets. For example, fix critical issues in 48 hours. Track mean time to remediate. This is core to how to audit source code with accountability.
Fix Fast: Remediation and Verification
An audit that does not lead to fixes has little value. Create tickets with owners. Add tests with clear steps.
For each fix:
- Reproduce the bug with a failing test
- Apply the fix with least risk
- Add guardrails in lint rules
- Re-test and close
I keep a shared doc of anti-patterns we banned. It speeds code review. It also teaches new devs how to audit source code as they code.
Build Audits Into CI/CD
Shifting left makes audits fast and cheap. Add checks to pull requests. Run deep scans on main at night.
Do this:
- Run SAST, SCA, and secrets scans on PRs
- Block merges on critical issues
- Publish nightly reports to chat
- Rotate rules and update tools often
This is the most reliable way to scale how to audit source code in big teams.
Legal, Compliance, and Supply Chain
Audits also protect the business. Check licenses in third-party code. Track SBOMs for products. Monitor vendor risk.
Map rules to standards. Use controls from common security guides. Note gaps and plans. This builds trust with buyers and regulators.
When you define how to audit source code for compliance, write down proof steps and store them.
Tools and Checklists
Pick a small, well-tuned toolset. Avoid tool sprawl. Keep one source of truth for results.
Helpful items:
- One SAST and one SCA that fit your stack
- A secrets scanner
- A linter with security rules
- A simple audit checklist by area
- A shared false-positive registry
A good checklist is key to how to audit source code with speed and with less noise.
Common Mistakes to Avoid
I see the same traps in many teams. Skip them to save time.
- Relying only on tools and ignoring manual review
- Auditing all code at once with no risk filter
- No threat model or data flow map
- No triage, so teams drown in alerts
- No follow-up testing after fixes
If you are new to how to audit source code, start with one service. Learn. Then expand.
Real-World Mini Case Study
A fintech team asked how to audit source code for a payment API. We scoped one repo and one flow. We ran scans and did a deep dive on auth and money moves.
We found a logic bug in refunds. A user could replay a call and double claim. The fix added idempotency keys and strict checks. We added tests and a linter rule. The team then used the same method for six more services. That is how to audit source code with real value.
Frequently Asked Questions of how to audit source code
What is the difference between a code audit and a code review?
A code review checks style and logic for quality. A code audit focuses on security and risk with proof and tests.
How often should I audit source code?
Do light checks on every pull request. Run deeper audits for each release or after big changes.
Which tools should I use to audit code?
Use one SAST, one SCA, a secrets scanner, and a linter. Pick tools that support your language and CI.
How do I reduce false positives?
Tune rules, suppress at the source, and keep a shared registry. Pair tool alerts with manual checks.
Can small teams do effective audits?
Yes. Start with checklists and a few tools. Focus on high-risk areas and grow from there.
What skills do auditors need?
They need secure coding, threat modeling, and strong reading skills. They also need to write clear reports.
How do I prove fixes worked?
Reproduce the bug, write a failing test, apply the fix, and re-run tests. Keep evidence in tickets.
Conclusion
A strong audit blends tools, checklists, and human insight. Start small, focus on risk, and ship fixes with tests. Make it part of your daily build so trust grows over time.
Take the first step today. Pick one repo and run the eight-step plan. Subscribe for more guides, templates, and deep dives on how to audit source code that drive real results.