Monitor logs, network traffic, and user behavior to catch intrusions early.
If you want to master how to detect server intrusion attempts, you need a sharp eye, the right tools, and simple habits that you follow every day. I’ll walk you through how to detect server intrusion attempts in real time and at scale. I’ve built and tuned these methods in real-world teams, under real pressure, and I’ll share what works, what fails, and how to avoid costly mistakes.
What counts as a server intrusion attempt?
An intrusion attempt is any action that tries to break your server’s rules. It might be a bad login, a strange script, a port scan, or data theft in progress. The goal is to spot it before damage spreads.
If you are asking how to detect server intrusion attempts, start with a clear map of what “normal” looks like. Then watch for anything that bends or breaks that pattern. Use alerts that flag odd spikes, new processes, and failed auth storms.
Early red flags you can’t ignore
Most attacks show hints before they land. Map these signals to quick checks. In practice, this is how to detect server intrusion attempts fast.
- Sudden bursts of failed logins from one IP or many IPs at once.
- New admin users or role changes without a valid ticket.
- Unknown processes using high CPU, memory, or network.
- Odd listening ports or services you did not install.
- Strange outbound traffic to rare countries or new domains.
- Web server errors that spike, like many 401, 403, or 500 codes.
- File changes in system paths or web roots at odd hours.
Log signals to watch across the stack
Logs tell the story. Keep them central, parsed, and searchable. If you want a reliable plan for how to detect server intrusion attempts, start with these log types.
- Auth logs. Track failed and successful logins, MFA denials, and sudo use. Alert on impossible travel and many failures.
- Web logs. Look for SQL errors, LFI/RFI tries, and long user agents. Flag paths like wp-admin, phpMyAdmin, or .env.
- System logs. Watch for kernel messages, service restarts, and cron edits.
- App logs. Focus on permission errors, token fails, and odd API calls.
- Database logs. Look for data dumps, DROP or GRANT commands, and wild SELECT patterns.
Simple queries help:
- Count failed logins per IP per minute. Alert on spikes.
- Track new user creation events by service. Alert when the actor is not a known admin.
- Watch for repeated 404s on risky paths, then a 200 on the same route.
Network clues: from scan to exfiltration
Network data shows intent. It is vital for anyone exploring how to detect server intrusion attempts.
- Port scans. Many small TCP handshakes across many ports. That is casing.
- Lateral movement. New SMB, RDP, or SSH links to peers that never talk.
- DNS oddities. Long, random subdomains or a flood of TXT lookups.
- Exfil signs. Large data to rare IPs or new countries. Alert on high egress volume.
- Beaconing. Small, steady outbound calls on fixed intervals.
Practical tips I use:
- Keep simple allow lists for egress. Block and alert on the rest.
- Build flow logs for VPCs or VLANs. Sample if you must, but keep enough detail.
- Tag crown-jewel servers. Give them tighter rules and finer alerts.

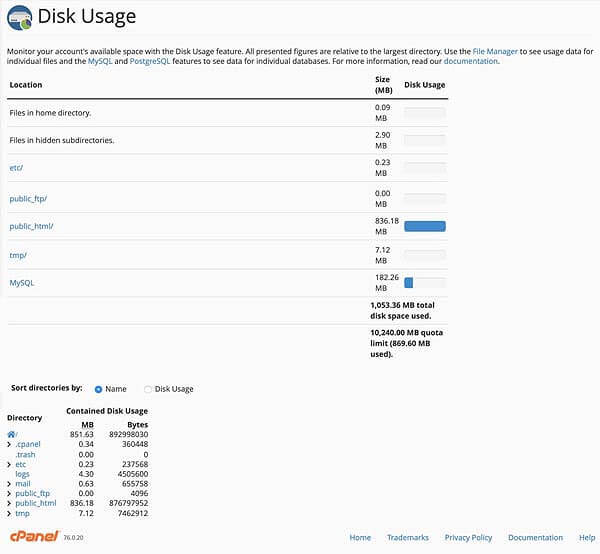
style="max-width: 100%; height: auto; border: 2px solid black; border-radius: 10px; display: block; margin: 0 auto;"
loading="lazy"
/>
Host telemetry: processes, files, and integrity
On the host, truth beats guesses. To learn how to detect server intrusion attempts on endpoints, watch for these changes.
- New binaries in /tmp, /var/tmp, or user home folders.
- Shells launched by web servers or databases.
- Cron jobs or systemd services added without a ticket.
- File integrity changes on key paths like /etc, web roots, and config dirs.
- Unusual kernel modules or drivers.
What works well:
- Enable process auditing and command logging on admin shells.
- Use FIM to hash files and alert on changes.
- Keep EDR agents up to date. Tune rules to your stack.
Identity and access anomalies
Accounts are a favorite door. If you want a clean way for how to detect server intrusion attempts at the identity layer, focus on context.
- Impossible travel. Two logins from far places in minutes.
- Time anomalies. Admin action at 3 a.m. when that user sleeps.
- MFA fatigue. Many push prompts or repeated OTP failures.
- Privilege jumps. User gets admin rights without a change request.
- Service accounts. They should not log in from human devices.
Tips I’ve used:
- Add geovelocity checks to auth logs.
- Correlate tickets with role changes. No ticket, no change.
- Lock and rotate keys on any hint of abuse.
Tools that boost your view: SIEM, IDS, EDR, NDR, WAF, and honeypots
You do not need a giant stack to start. But the right mix makes it easier to learn how to detect server intrusion attempts.
- SIEM. Central log search, correlation, and alerting. Use it for rules and cases.
- IDS/IPS. Catch known attack patterns on the wire. Tune to your traffic.
- EDR. Deep host view, process trees, and quick isolate actions.
- NDR. Network behavior analytics. Great for lateral move and exfil.
- WAF. Blocks common web exploits and gives clear signals.
- Honeypots. Low risk, high signal. Attackers touch them first.
Make them work together:
- Send alerts to one place with context.
- Auto-tag assets by role and criticality.
- Build simple playbooks to cut delay.
Build baselines, then write alert rules
You cannot alert on “weird” if you do not know “normal.” This step is key in how to detect server intrusion attempts with low noise.
Steps I follow:
- Observe normal logins per hour per system for 14 days.
- Record average web errors by path and method.
- Measure normal egress per host, by protocol and country.
- Set thresholds with some cushion. Use sliding windows.
- Add suppression for known noisy jobs.
Rule ideas that work:
- X failed logins from one IP in Y minutes.
- New process spawned by a web server that runs a shell.
- First-ever connection from a host to a new ASN or country.
- FIM change on protected paths outside maintenance windows.
Fast triage: validate, contain, confirm
Speed matters. A simple flow helps you practice how to detect server intrusion attempts and act before they spread.
Do this when an alert fires:
- Validate. Check two sources. For a login alert, confirm IP, user, and time.
- Contain. Isolate the host or block the IP if the risk is high.
- Confirm. Pull process lists, netstat, and relevant logs.
- Decide. Escalate, close as benign, or watch with tighter rules.
Personal tip:
- Keep a short checklist and scripts ready. When stress hits, simple wins.
Real-world stories and simple playbooks
These short cases show how to detect server intrusion attempts with clear steps.
Case 1: Web shell on a CMS
- Signal. Spike in 500 errors, then odd POST to upload.php.
- Check. New file in wp-content with random name, owned by www-data.
- Act. Quarantine server, collect the file, rotate secrets, patch plugin.
Case 2: SSH brute force to a Linux host
- Signal. Many failures from many IPs, then one success.
- Check. Who logged in, from where, and what commands ran.
- Act. Disable password auth, enforce keys and MFA, add fail2ban, rotate keys.
Case 3: Crypto miner dropped via misused sudo
- Signal. CPU pinned, new process called kworker-like, outbound to pool.
- Check. Cron change and new binary in /tmp.
- Act. Kill process, remove cron, reimage if trust is lost, close sudo gap.
Metrics that matter
Track what improves. It keeps you honest and helps explain how to detect server intrusion attempts to leaders.
- Mean time to detect. From first sign to first alert.
- False positive rate. Are you wasting time?
- Coverage. Percent of assets with logs, EDR, and baseline.
- Detections per category. Auth, web, network, data exfil.
Build a small weekly report. Show trends and wins. Adjust rules when noise grows.
Common mistakes to avoid
The path to learn how to detect server intrusion attempts has traps. Here are the big ones I’ve seen.
- Logging is off or too thin. Fix retention and fields before fancy rules.
- No inventory. You cannot monitor what you do not know exists.
- Alert floods. Too many alerts numb your team. Tune or disable weak ones.
- Ignoring egress. Many teams watch inbound only. Data walks out the back.
- Skipping reviews. Rules rot. Revisit them each quarter.
Hardening that makes detection easier
Strong defenses make signals clearer. It also shortens the list of ways in. This supports your plan for how to detect server intrusion attempts.
- Least privilege. Fewer admin rights, fewer chances to abuse.
- Patch fast. Shrink the exploit window with simple patch cycles.
- Network segmentation. Limit blast radius and make odd traffic pop.
- Secure defaults. Disable unused services and default creds.
- Backups and test restores. If the worst hits, you come back quick.
Frequently Asked Questions of how to detect server intrusion attempts
What is the best first step for small teams?
Start with central logs and simple alerts on failed logins, new users, and web errors. Add EDR on critical servers and tune from there.
How can I reduce false positives?
Build baselines for normal behavior and add suppression for noisy jobs. Review alerts weekly and remove weak rules that never catch real risk.
Do I need a SIEM to detect attacks?
No, but it helps. You can start with open logs, simple queries, and scripts, then move to a SIEM when scale demands it.
How often should I review detection rules?
Do a light review each week and a deep review each quarter. Update rules after any incident to capture new patterns.
What data should I keep for forensics?
Keep auth logs, web logs, process and file change logs, DNS logs, and flow records. Retain at least 30–90 days, longer for key systems.
Conclusion
You now have a clear path for how to detect server intrusion attempts with simple steps, smart tools, and fast triage. Start with logs, add network and host signals, then tighten rules with real data. Keep it practical, keep it calm, and improve a bit each week.
Take one action today: add an alert for failed logins and a baseline for egress. If you found this useful, subscribe for more guides, share with your team, or leave a question so we can go deeper together.